In this article
Tired of being in the cyber sec vendor pitch merry-go-round? Confused as to why you need to replace the product you purchased last month because this month’s product is more “innovative.” Has your CISO called to ask “so do we really need XDR if we have a SIEM?” and you don’t have a clear answer?
The most frustrating part is that the right, logical tools actually exist with real individual value for the right use cases. And XDR, SIEM, SOAR are just a few of the key products that you encounter when it comes to security platforms.
But the reality is the descriptions of these tools are so vague, and the marketing speak is so similar that they almost sound identical. Every vendor claims that their product will “detect”, “respond”, and “protect” against threats using “AI-powered” and “Advanced Machine Learning” capabilities, but it feels like it is all just marketing fluff.
At TechBrain, we help Australian businesses cut through that fog every day. Our cyber security team deploys and manages these platforms across a wide range of industries, so we know firsthand where each one delivers real value and where the marketing outpaces the reality. This guide is built on that hands-on experience.
In Brief
- XDR (Extended Detection and Response) deals with active threat detection and automated response across endpoints, cloud, email, network, and identity. It’s ideal for businesses that need speed and consolidated visibility.
- SIEM (Security Information and Event Management) handles log aggregation, compliance reporting, and long-term data retention. It’s essential for businesses dealing with compliance requirements such as APRA CPS 234, the Privacy Act, ASD Essential Eight, as well as cyber insurance obligations and contractual security requirements from clients and partners.
- SOAR (Security Orchestration, Automation and Response) ever wish you could automate the response steps between detection and human action through predefined playbooks? SOAR solves that and the hot trend is its native adoption into XDR platforms.
- Typically, Australian businesses work with a provider like TechBrain to deploy two or all three of these platforms in combination. Finding the right mix depends on your organisation’s size, compliance obligations, security maturity, and SOC staffing.
- If you’re a lean SMB, engaging a managed security partner to select and run the right platform for your needs is the most practical path. If you’re regulated, SIEM is non-negotiable. If you’re a mature enterprise under active threat, you’ll want both XDR and SIEM working together.
So here’s the real question: which ones are you supposed to be running?
XDR, SIEM, and SOAR: What Each Platform Actually Does
XDR (Extended Detection and Response)
XDR means you can integrate telemetry from endpoints, cloud workloads, email gateway, network and identity systems into a single platform. Do you have five security products producing five separate alert streams for your team to manage and correlate manually? XDR integrates most of those sources into a single, correlated view of an attack that spans multiple surfaces.
We say “most” because no XDR product covers everything, for example, CrowdStrike’s XDR currently has limitations integrating with certain vendors like WatchGuard. The depth of integration depends on whether you’re running a native or open XDR architecture.
If you’re familiar with EDR, you’ll appreciate what managed XDR brings to the table. EDR (Endpoint Detection and Response) is great at one thing: monitoring endpoints. But it only does that one thing. XDR is the next step up, extending that visibility across the entire environment.
So here’s a scenario that could play out. Let’s say a user in finance clicks on one of the usual Tuesday phishing emails. The laptop is compromised in a matter of minutes and the attackers are then able to start moving laterally on the network, poking around shared drives.
In this case we’re looking at three of our security layers being triggered by a single attack. The EDR on the laptop detects the compromise and flags it. That’s all it can see though. It can’t see the original phishing email that kicked off the attack, nor the lateral movement as it spreads across network segments. An XDR platform would see the entire attack as a single, fully correlated incident and would be able to automatically contain it.
You’ll hear vendors talking about “native” XDR, where the XDR product is a component of a security suite provided by a single vendor. Everything works out of the box, but that vendor always has a closed ecosystem. In “open” XDR, the product gathers information from sources across different security vendors. Open XDR can collect from a wider range of sources, but it is generally more complex to deploy and manage.
XDR offers more automation capabilities than traditional platforms, leveraging machine learning and behavioural analytics to automatically correlate activities, assign risk scores and respond with containment actions that block newly identified threats without requiring the team to intervene.
Adoption is accelerating on a global scale too. Gartner’s 2024 Market Guide for Extended Detection and Response projects that by 2028, 30% of end-user organisations will deploy XDR to consolidate security vendors, up from less than 5% today — a trajectory that reflects just how fragmented the average security stack has become.
SIEM (Security Information and Event Management)
SIEMs have been a core component of the security stack for years, and in most cases here in Australia are required by compliance.
So what does a well-managed SIEM actually do? It collects security logs from systems across your environment, normalises them into a standard format, correlates the events, validates them against frameworks like MITRE ATT&CK, allocates threat levels, and classifies incidents. A properly configured SIEM is actually the foundational layer on which XDR, MDR, SOC, and SOAR all operate.
If you are required to meet compliance requirements such as APRA CPS 234, Privacy Act 1988, ASD Essential Eight, cyber insurance mandates, or contractual security obligations, then you probably already have a SIEM deployed. SIEMs are the one control that can consume such a broad range of logs, provide long term storage of the data for auditing, and deliver the mandated reporting required by regulators.
Now, SIEM has a reputation problem and it’s not entirely undeserved. Organisations that deploy a SIEM without the right expertise to manage it often end up drowning in alert storms, false positives, and correlation rules that never get tuned.
Look, in our experience that’s not a platform problem, that’s a problem with the operator… any tool in the wrong hands can be plainly ineffective. Thankfully, with the right hands SIEM can be a powerful and effective platform, it’s the type of problem TechBrain solves for clients every day, making it work properly so you’re not wasting analyst time chasing noise.
Newer SIEMs are starting to incorporate User and Entity Behaviour Analytics (UEBA) and machine learning to help surface genuinely suspicious activity rather than flooding analysts with irrelevant noise.
Even with the newest shiny features, some things never change. SIEM’s greatest strength remains its unmatched breadth of visibility, compliance capability, and its role as the data backbone for the rest of your security operations.
SOAR (Security Orchestration, Automation and Response)
Everyone knows that there is always a long period between realising there is a problem and actually doing anything about it. A SIEM or XDR system may detect an issue by reporting that something does not look right. The SOAR system will then take the initiative to decide what to do about it and automatically execute the steps outlined in a playbook to remediate the issue: isolate a compromised host, block an IP address, check a threat feed, then escalate to the appropriate resource.
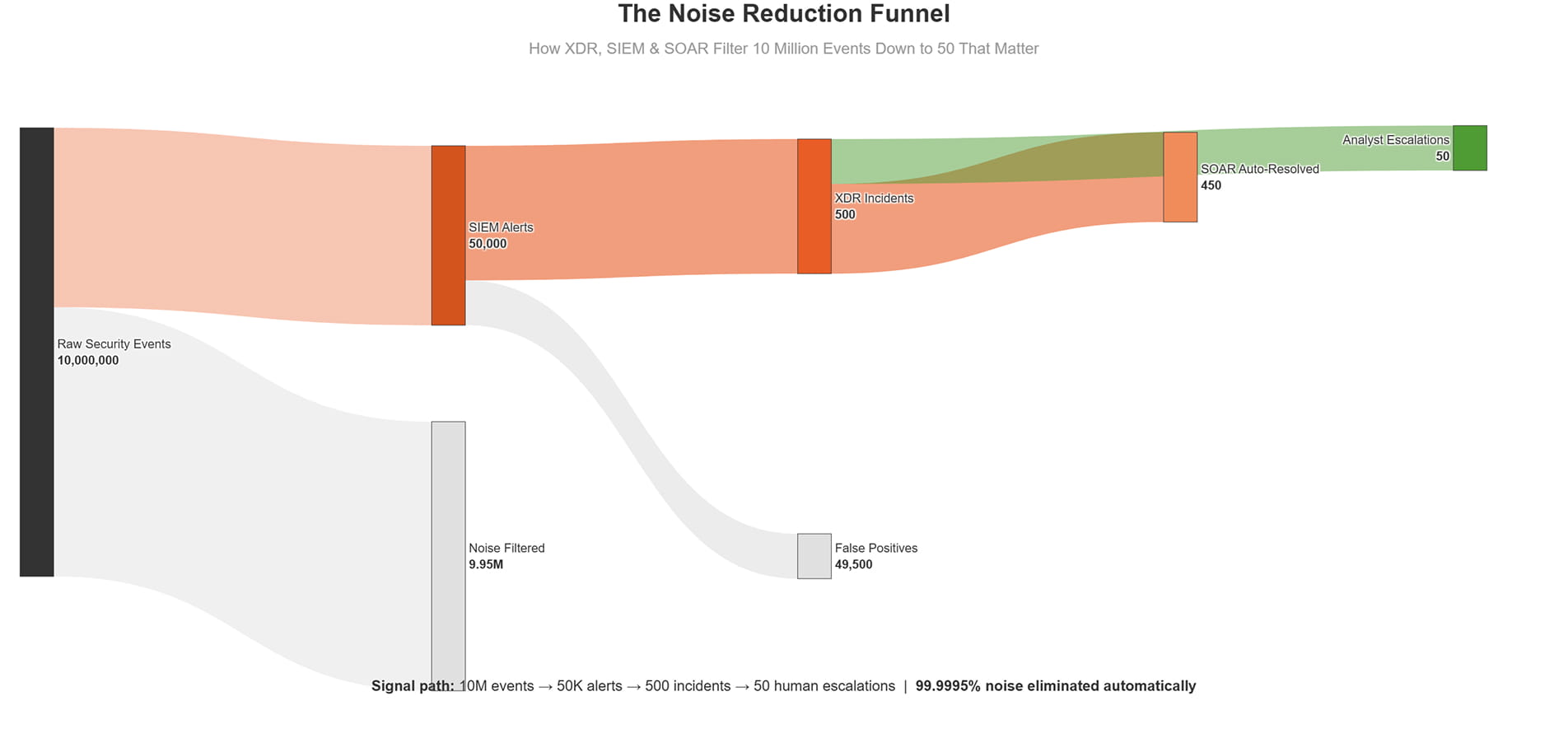
I just wanted to clarify one thing. SOAR does not detect threats. It’s simply a tool that uses data from your SIEM and XDR systems. SOAR is a product category that evolved to address two major pain points: we’ve all been bombarded by thousands of irrelevant alerts, and there are not enough people who can deal with them efficiently.
Unfortunately this is a global problem, and here in Australia we have the added complexity of a severe cyber skills shortage.
But there are a few factors impacting the SOAR conversation. Many XDR products are starting to include the capabilities that you used to need a separate SOAR product for.
Automated response workflows, playbook-based orchestration, cross-tool automation. If your XDR product is doing its job of automatically containing and escalating threats, why would you spend money on a SOAR product as well?
Head-to-Head: XDR vs SIEM vs SOAR Comparison
| Dimension | XDR | SIEM | SOAR |
| Primary purpose | Detect and respond to threats | Aggregate logs, detect anomalies, support compliance | Automate and orchestrate response actions |
| Data sources | Endpoint, cloud, email, network, identity (deep but ecosystem-dependent) | Virtually any log source (broad but less deep) | No native data collection; relies on SIEM/XDR inputs |
| Detection method | ML-driven behavioural analytics and cross-layer correlation | Rule-based correlation with emerging UEBA/ML capabilities | No detection; executes response based on triggers |
| Response capability | Built-in automated response actions | Limited; generates alerts for analyst triage | Playbook-driven automation and orchestration |
| AU compliance fit | Not designed for long-term log retention or audit reporting | Strong fit for APRA CPS 234, ASD Essential Eight, Privacy Act | Supports compliance workflows but not a compliance tool |
| Staffing needs | Lower; reduces analyst decision overhead | Higher; requires dedicated tuning and triage resources | Moderate; requires playbook development and maintenance |
| Deployment complexity | Moderate; tighter within native vendor ecosystems | High; significant tuning and integration effort | Moderate to high; integration with existing tools required |
| Cost model / TCO risk | Vendor lock-in risk with native XDR | High ongoing tuning and storage costs | Licensing plus integration costs; value depends on alert volume |
Detection Speed
This is where the gap between XDR and SIEM is at its widest. XDR brings together events from across all layers of your IT environment, prioritises what’s most important, and delivers actionable alerts when you need them. With SIEM, you get more granular, unfiltered data for detailed forensic analysis, but it’s often too slow for real time incident response.
The numbers clearly tell the story. Based on the IBM Cost of a Data Breach Report 2025, security teams using AI and automation extensively shortened their breach lifecycle by 80 days and lowered average breach costs by USD $1.9 million. That’s not a small number. It is the difference between having a security incident that stays under control, and having one that becomes a media sensation.
Compliance
APRA regulated entity? This section is for you. CPS 234 requires regulated entities to have controls in place commensurate with the level of risk presented to their organisation, and that includes adequate logging and monitoring. SIEM systems are designed to store logs long term, capture a full audit trail, and provide the required reporting for regulatory compliance. XDR is for real time detection and response and is not built for long term log storage.
We also need to talk about the SOCI Act. Critical infrastructure entities are now required to report significant cyber incidents to the ASD within 12 hours, with a further 72 hour window for other reportable incidents. To get all the information to ASD in that 12 hour window you’ll need the automated response power of XDR and SOAR.
For the post-incident forensic trail you’ll need a SIEM. Remember that energy, utilities, financial services and healthcare all fall into the critical infrastructure category, so if that’s your sector you’ll likely need both.
Data Coverage
SIEMs consume and monitor logs from almost any source you can imagine. Routers, firewalls, applications, cloud systems, on premise servers and legacy systems. XDR looks at a broader set of security-relevant sources but those sources are limited to what the vendor chooses to include in their product.
Most Australian organisations have a hybrid environment, some legacy on premises systems and some in the cloud in AWS or Azure. The practical approach tends to be a SIEM to give a broad view of the environment, and XDR to give a deeper view.
XDR, SIEM, or Both? Choosing the Right Platform for Your AU Organisation
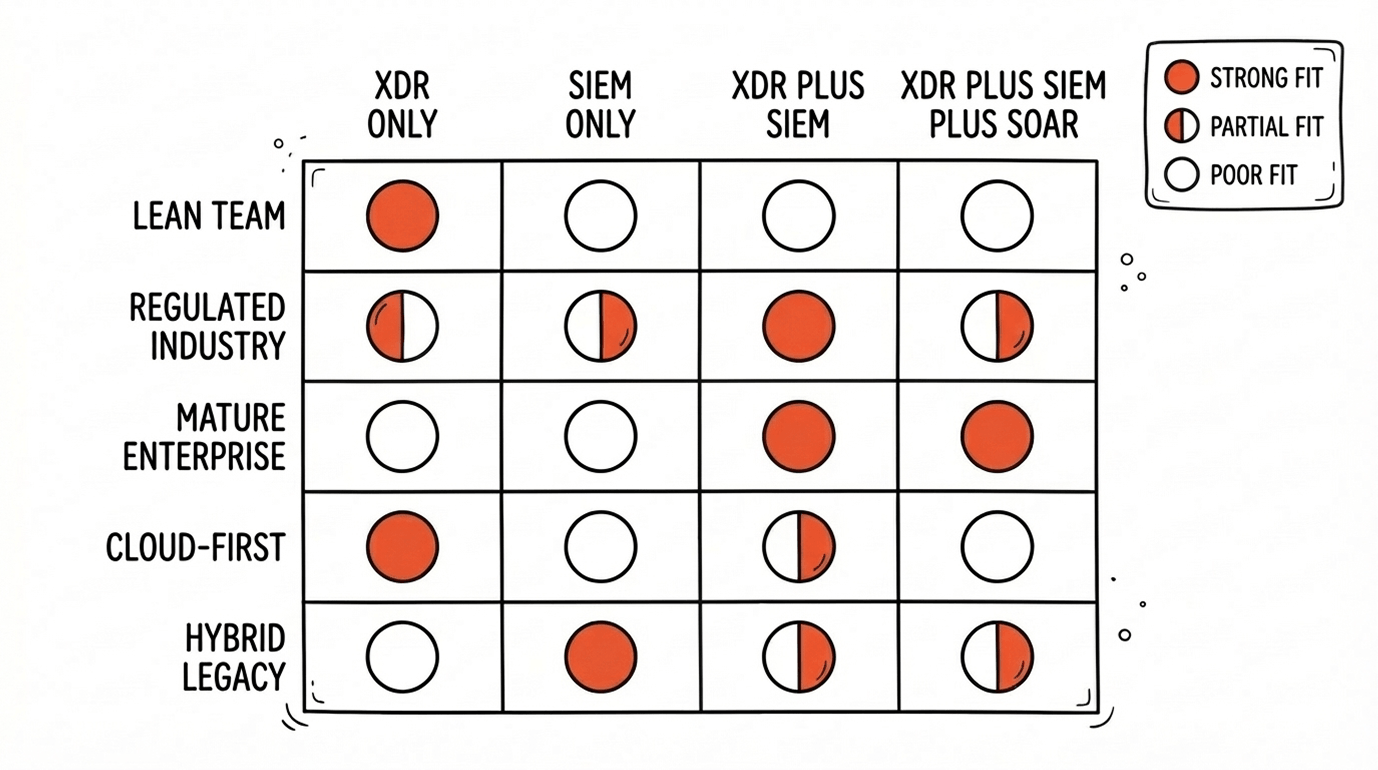
Five factors influence this decision: organisation size, security maturity, compliance obligations, SOC staffing and budget. There isn’t a right or wrong answer, but here are a few trends and patterns we’ve seen working with Australian businesses across a range of industries.
Lean security team, early-stage maturity
With the exception of particularly sophisticated or targeted attacks, XDR has proven to be enough to effectively protect many mid-market businesses. It combines threat detection, correlation and response in one platform, making a full SOC team unnecessary. For most organisations at this stage, engaging a managed security partner like TechBrain to select, deploy, and run the right platform is the most practical and cost-effective path.
Growing compliance burden
With APRA CPS 234 and ASD Essential Eight requirements that include logging obligations, SIEM is no longer an optional control. Central event logging is a fundamental component of Essential Eight auditing, and the retention and reporting controls required by regulators far exceed what an XDR solution can provide.
Mature enterprise with active threats
Run both. We highly recommend running XDR and SOAR for immediate, automated detection and containment. Then use SIEM to hold the forensic trail with longer term storage and for compliance reporting. This is fast becoming the standard position for many enterprises in Australia.
When XDR Is the Right Choice
- The security team is small. Analyst time is scarce.
- Getting to threats fast matters more than generating compliance reports.
- You want to consolidate EDR, NDR, and email security into one platform.
- Your environment is mostly cloud-based.
When SIEM Is Non-Negotiable
- Regulated by APRA, Privacy Act, or ASD. Full stop.
- You’ve got a mature SOC with analysts who can handle tuning and triage.
- Your environment is messy. On-prem legacy systems sitting next to cloud infrastructure, different vendors across the stack.
When You Need Both
- Large enterprise juggling compliance obligations alongside real-time threat response.
- SIEM does the compliance logging and retention. XDR does the detection and response.
- Most common integration pattern: XDR feeds high-fidelity alerts into SIEM for archival.
- You need the budget and staffing to support two platforms. There’s no getting around that.
Expert Insight: Ashish Srivastava, Head of Cyber Security at TechBrain
“What we see time and again is that Australian businesses want the outcome. They want to know they’re covered, compliant, and that someone is actually managing their security. How the work gets done behind the scenes is TechBrain’s problem to solve, not theirs.
In practice, yes we run SIEM, SOAR and XDR together. But the real value for clients isn’t the tech stack — it’s that they don’t have to think about it. They get the compliance coverage that SIEM provides, the automated response that SOAR delivers, and the cross-environment visibility that XDR brings, without having to hire three separate specialists or manage three separate vendor relationships.
That’s what partnering with a provider like TechBrain gives you. Businesses get the full capability of a mature SOC without having to build one themselves.”
Not sure where your stack has gaps? TechBrain’s Security Platform Assessment maps your existing environment and identifies whether XDR, SIEM, or a managed service is the right move, without the vendor bias.
Future Trends: Where XDR, SIEM, and SOAR are Heading
These categories are merging. Microsoft Sentinel and Google Security Operations already combine SIEM, XDR, and SOAR capabilities into single platforms. AI is accelerating detection and response on both sides. Cloud-native SIEM is stripping out the on-prem overhead that made traditional SIEM so painful to deploy and maintain.
The bigger picture is consolidation. The days of stitching together eight different point products are numbered. Fewer platforms, broader capability, less integration headache.
For Australian organisations specifically, this trend is being pushed along by a skills shortage that isn’t going away any time soon. The ISC2 2023 Cybersecurity Workforce Study puts Australia’s cybersecurity workforce gap at roughly 28,000 professionals. That makes it genuinely difficult to find the people you’d need to run standalone SIEM and SOAR deployments in-house.
Which brings us to MDR. Managed Detection and Response wraps 24/7 managed operations around your XDR or SIEM. Monitoring, threat hunting, incident response, all delivered as a service. For teams that can’t hire fast enough, it’s the most practical path forward.
How TechBrain Helps
Here’s the thing most businesses figure out eventually: you don’t actually need to choose between XDR, SIEM, and SOAR yourself. You need someone who runs all three and gives you the outcome.
That’s what TechBrain’s vCISO and Managed SOC services are built for. We act as a SOC for your XDR, SIEM, and SOAR, managing your tools as one integrated service to deliver compliance coverage, automated response, and single-source visibility. No need to fund three specialty hires or juggle three separate vendor relationships. One team to manage, one conversation to have, one bill to pay.
We can also assist organisations not currently operating under a full SOC model to help them get there:
- Security Platform Assessment: We assess your current stack end to end, identifying gaps, overlaps and the appropriate XDR/SIEM architecture for your organisation’s size, compliance requirements and SOC maturity.
- Managed XDR: 24/7 monitoring, threat hunting and incident response for organisations without an in-house SOC.
- SIEM Optimisation and Management: Rule tuning, rule development, and ongoing managed operations to reduce false positive volume and improve detection accuracy. Particularly valuable for organisations under APRA CPS 234 requirements.
- ASD Essential Eight Advisory: Assessment and uplift aligned to the Essential Eight maturity model, focused on the logging and monitoring controls that feed directly into SIEM and XDR decision making.
Book a security platform assessment to get a recommendation built around your environment and compliance requirements, not around what a vendor wants to sell you.