In this article
Cyber security threats
When it comes to cyber security threats for medium businesses, there are a number of common threats to be aware of. Below are some of the top cyber security threats facing SMB’s in 2021, as recorded in the Australian Cyber Security Centre report.

Ransomware
Ransomware is one of the biggest threats against medium sized businesses, and has evolved over the years.
It’s one of the biggest threats as it’s just so prevalent. Cybercriminals will trick the user into downloading a file, or clicking through to a particular link, that then automatically downloads the malware and installs it on their computer.
Then, once installed, the malware will begin to encrypt specific files on the computer. This locks you out of the files, denying access—and then you receive an on-screen alert, telling you that your sensitive data has been encrypted.
Attackers will then demand a ransom in order to release the files back to the user. This is typically done in Bitcoin and other cryptocurrencies these days.
If no ransom is supplied, these files are then deleted forever.
Given our increased reliance on data, it’s a tricky situation to be in. Ransomware extortions have ranged from thousands of dollars, up to millions, depending on the business in question.
And while cybercriminals understand that smaller businesses can’t cough up those higher figures, they know that it’s still a lucrative field to target—SMB’s live and die depending on their data.
Zero-day vulnerabilities
Zero-day vulnerabilities are a big target for cybercriminals. And what’s worrying about this type of attack is that you often have no way of stopping it.
A zero-day vulnerability occurs when a weakness or a vulnerability is discovered in a certain system or piece of software.
It’s so-called, as this weakness is discovered by cybercriminals first, before the vendor is made aware of it. They have zero days to respond—hence the name. Cybercriminals can then exploit these vulnerabilities to access entire systems.
The results will all depend on what they want to achieve. It may be gaining access to a particular business system to retrieve sensitive information.
It might be infiltrating a specific program and injecting malicious code, or install software, to make use of at a later date. It could be entering a business’ system to gain important data and customer information. Or it could simply be to cause havoc.
Data Breaches
Any security breach can create a major headache for a company because it can cause you to lose trust and respect from your customers. But it’s important to remember that it happens to everyone, even big companies like Equifax and Yahoo.
You can reduce your chance of getting hacked by using security software and changing your passwords often, or consulting external cyber security experts.
Customer information commonly leaked includes names, addresses, email addresses, telephone numbers, account information, and in some cases, encrypted passwords.
With the introduction of new GDPR standards protecting customer information has never been more important and it’s going to affect a lot of companies and a lot of individuals.
You need to make sure that you’re focusing on data security and that your website is compliant with the GDPR. A lot of people forget that it’s not just the customer’s data you should be protecting, it’s yours too.
If you’re storing customer data on the same servers as the rest of your company, make sure you’re encrypting your customer data and offering them encryption storage.
It’s important to have a security strategy, even if you’re a solopreneur. Security is a big concern for all business owners, but it’s especially important if you have a company that deals with sensitive data.
Exploitation of our increasingly connected world
As more and more Australians are taking advantage of flexible working arrangements, cybercriminals have moved to take advantage of this.
Our email use is increasing, and so too is the instance of business email compromise—and phishing scams.
Hackers are getting better at infiltrating business emails, gaining access by pretending to be from legitimate users or external sources, and gaining unwitting users’ credentials, passwords, and personal information.
And, unfortunately, as our use of email and online communication tools grows, so too does our complacency. We’re so used to existing online, in and out of our emails, that our caution is slipping.
Cybercriminals are taking advantage of this—and evolving how they perform cyber attacks. They’ve gone beyond the random, easy-to-spot phishing scam, and moved on to more targeted phishing emails, known as spearphishing.
Spearphishing typically involves hyper-targeted scam emails pretending to be from legitimate sources, much more carefully engineered than the broad-brush phishing emails we’re used to.
An unsecure link here, a surprise download there, and cyber criminals can cause havoc on a business system.
SMB cyber attack examples
One of the most concerning cyber attack examples for SMB’s in recent history was the Microsoft Exchange server zero-day vulnerability cyber attack.
It wasn’t particularly damaging in its immediate effect, but its reach was particularly worrying, and demonstrated the expansive nature of online threats around today.
What is the Microsoft Exchange Server hack?
In March 2021, four previously unknown vulnerabilities were discovered in the Microsoft Exchange server. This was particularly troubling, as it’s one of the most popular cloud services, with an extraordinary amount of businesses relying on this server.
Over 30,000 businesses and organisations were affected by this vulnerability, with potentially thousands more also affected.
The hackers in question, known as HAFNIUM, used these vulnerabilities to access the in-house exchange servers of their victims, accessing company emails, and installing malware that would effectively leave a backdoor entrance for future access.
Microsoft has since created a patch for these vulnerabilities, moving quickly to neutralise the threat.
But, really, it was already too late. Hackers and cybercriminals had their chance to access unsecured networks and deploy ransomware and other malicious software.
So it’s not just your business’ immediate systems and software that are vulnerable—it’s your entire IT ecosystem.
Our top 10 cyber security tips for SMB’s
For SMB’s, securing your network is the first critical step in arming yourself against cybercriminals. To help you achieve this, here are our top 10 SMB business cybersecurity tips to help medium business owners avoid cyber threats.
They may not be ground-breaking, but that’s not the point. They’re practical, and get the job done—which is what you really need. And when completed correctly, they work together to ensure your business’ network is as safe as possible.
Check your physical security first
Physical security is just as important as web security. And in some cases, it can even be your first barrier against threats towards your network.
Data breaches can be surprisingly low-tech, and can be as simple as leaving a bag on a train, or having an unauthorised person entering your office and picking up an unsecured tablet or smartphone they see lying around.
Physical security should be your first line of network defence. Ensure your business has the basics in place, like staff ID tags, security cameras, and tracking your mobile devices—and even business computers.
Ensure your WiFi is secured
An unsecured wifi connection can be a often the weakest link in defending against cyber attacks towards your business. Hackers can compromise public networks easily, providing a quick way to infiltrate your business’ network.
So make sure your wifi network is password protected—with strong passwords, too—and access is limited to only the right users. And if you offer free guest wifi, make sure it’s a different network to the one your business users use.
Update your antivirus software and firewall software as often as possible
It should be obvious, but it’s astounding at how many business users forget this. Updating your antivirus and business firewall software ensures that you’re protected against the latest identified cyber threats.
Many platforms perform automatic updates. But others you may not think about: things like the firmware in your wifi router, printers, and other remote devices. These need to be updated manually.
And it’s not just your security software. Updating your operating system, your internet connection security, and every application and platform that you use ensures that every one has the latest software patches available.
Back up everything regularly
If you fall victim to a ransomware threat, while an annoyance to deal with, having your vital data backed up means you can simply roll it back from the latest backup, rather than losing the whole lot.
So performing regular data backups ensure that your business’ digital information is always as up to date as possible.
Having this backup data and critical information available safely and securely ensures you’re able to get up and running sooner in the event of a cyber incident.
Deploy a VPN
With the pivot to remote work, many businesses are already operating with a VPN. But for those that aren’t, it’s still a necessary tool in the fight against cybercrime.
A VPN is a virtual private network. It’s exactly what it sounds like: a tool that creates a secure, private, and encrypted network that only authorised users can access.
It ensures the sensitive data on your business network remains safe, and can only be viewed by users on that network.
Set up multi factor authentication
You’ve probably got two-step authentication, or multi factor authentication, set up for your personal banking or emails.
But what about your business logins? Setting up two-step authentication ensures your users always know who’s accessing their accounts, and can notify your cybersecurity team in the event any unauthorised activity occurs.
Monitor all BYO mobile devices accessing your network
Having a clear log of every mobile device being used on your network ensures you can control who has access. It’s a simple tip, but it works, and those with administrative privileges will know any time an unauthorised mobile device tries to gain access to your network.
Provide staff cyber awareness training
Regular cyber awareness training for your staff ensures that best practice cyber security protocols are always top of mind.
You can train employees on things like safe email use, how to spot fraudulent emails—even protocol around creating strong passwords. Unless they’re completely random, default passwords just don’t cut it.
Ensure the businesses you deal with have parallel security procedures
Ensuring your client, supplier, and customer networks follow similar security practices to you is important.
This way you get peace of mind that should they access your network, they’re just as secure on their end as you are on yours.
Manage user access
We’re not saying you need to completely restrict what your users can access on your network, but not everyone needs to have access everything, do they?
Creating limited access accounts, online accounts, and setting administrative privileges ensures that only the right people are able to see and use your critical data.
It also helps monitor users on your network, so be sure to delete any old user accounts for more secure results. While these tips are helpful, there’s more you can do to improve your business’ cybersecurity posture.
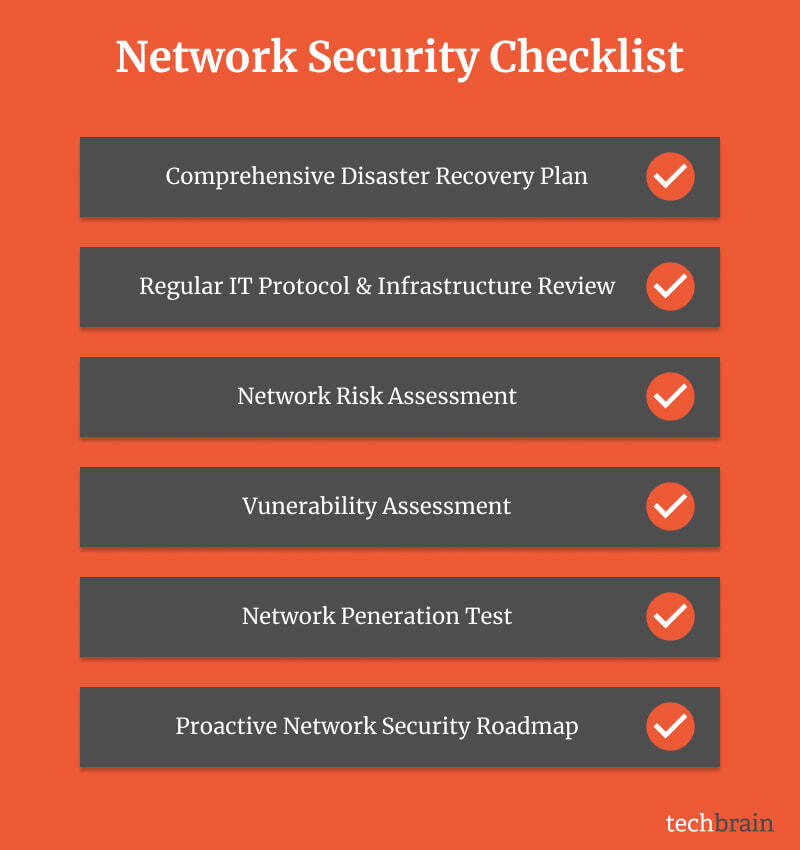
SMB Network Security Checklist
The practical tips above are things you can do right now, for the most part, to improve your business’ IT security posture. But for long-term network security for your medium business, we recommend you follow this checklist.
Have a comprehensive disaster recovery plan in place
Planning for the worst-case scenario ensures you’re prepared. So it’s critical that your business prepares a thorough disaster recovery plan.
It should include critical items like your data backup process, how to manage specific kinds of threats, and the specific steps to take should something go wrong.
Regularly review your IT protocols and infrastructure
Being aware of your current cybersecurity stance is the first step to understanding what needs improving. Performing regular IT audits performs two services.
First, it enables you to gain a full picture of your entire IT architecture. You’ll be able to understand the extent of your network, and what you have to secure.
Second, this audit will allow you to uncover any new gaps or vulnerabilities on your network, and give you clear pointers on what needs to be improved.
Undertake a risk assessment against your network
After mapping out your IT architecture and working out its extent, undertaking a risk assessment allows you to determine where any weak spots are.
More than just gaps in your security, a risk assessment enables you to determine the likelihood that any of the risks you’ve planned for actually occur.
It also helps you identify where your processes are lacking. Are there any disaster recovery practices you haven’t mapped out yet?
Perform a vulnerability assessment
A regular vulnerability assessment makes sure you’re aware of whether or not your current cybersecurity practices and protocols are robust.
It means you’ll be able to confirm that your security software has the latest patches, allows you to uncover flaws and gaps that haven’t been apparent in previous reviews, and identifies any potential access points to your network.
You’re trying to effectively flush out all the gaps in your network.
Network penetration testing
Once you’ve mapped out your IT footprint and identified any weaknesses, it’s time to put your security systems to the test.
In network penetration testing, a cybersecurity specialist will perform the role of a cyber criminal, and try and breach your IT security systems.
Anything they have at their disposal, they’ll use to try and gain access, much like a real hacking attempt. This enables you to determine just how vulnerable your network is to threats, and understand where your business needs to improve its practices, processes, and platforms.
Create a plan to improve your network security
You’ve identified the high risk areas of your network. You’ve mapped the vulnerabilities. You’ve put your IT security through its paces.
Now it’s time to collate all the information and draft a plan that takes all these into account, fixes them, and improves your network security posture.
It’s important to develop a strong strategic plan. In-fact, modern industry best practice often mirrors military strategy frameworks in an Observe, Orient, Decide and Act (OODA) response to cybersecurity incident response.
The recommendations that come out of your plan are the real IT checklist. Follow this, and your business will be as secure as possible.
Your secret weapon: Extra SME IT support
The reality is that you can only do so much to improve your business network security.
You can install an office firewall, update your anti virus software, deploy a VPN for remote connections, and initiate two-factor authentication—but for that extra layer of protection, IT security really requires specialist support.
Engaging the services of a specialist, experienced IT support and cybersecurity team will provide you with the best chance and ensuring your business remains safe and secure against external cyber threats.
They can augment your existing IT department, and ensure you remain safe against ransomware attack, data loss, and keep your confidential information confidential.
vCISO Support
You might be asking what is a vCISO? A virtual chief information security officer (vCISO), is a technology professional who provides guidance and leadership over a company’s cyber-security strategy without actually having to be a CISO.
Employing a vCISO is a great solution for companies that are looking to outsource their IT infrastructure.
By assisting in strategically deploying a broad range of it security services to help businesses with their infrastructure, including helpdesk, network monitoring, and network security.
In conclusion
TechBrain is a leading provider of innovative IT security solutions for SMBs. We know what it takes to ensure your business’s network security is secure, so you have the best chance possible against future cybersecurity threats.
Get in touch with us today to discuss your business’ network security, and organise a free consultation to discuss how we can improve your IT posture for the future.
After all, you never know what’s going to happen—so your best defence is being as prepared as possible.